Protect your data like Fort Knox
At DESelect, we prioritize compliance and take the security and privacy of our clients’ data seriously. To maintain this commitment, we undergo an annual audit to comply with ISO27001 standards, which is a globally recognized certification for information security management.
We rely on SOC 2 Type II compliant data centers. Being a SaaS company we are aware that we have shared security responsibilities, which are being defined using CSA star. DESelect is GDPR compliant, ensuring that we meet the strict data protection requirements set forth by the European Union. Moreover, we are CCPA & HIPAA compliant (as business associate).
Our servers are in secure data centers, managed by DigitalOcean, with ISO-27001:2013, SOC I and II, and PCI-DSS certifications.
At DESelect, we place a high priority on platform security, knowing that it is essential for the safety and privacy of our client’s data.
We are committed to providing a secure platform for our clients, which is why we continuously conduct security testing to identify and address any potential vulnerabilities.
By doing so, we ensure that our platform remains highly secure and protected against cyber threats. Our ongoing efforts in this area are aimed at providing our clients with the confidence and peace of mind they need to focus on their business without worrying about the security of their data.
In case you want to contact our DPO, please email to [email protected]
DESelect values the importance of our customers’ data, and therefore, we treat it with the utmost care and security (encryption and data backup) by implementing the best practices.
DESelect’s platform is cloud-native and highly scalable, allowing us to adapt to any situation and maintain a 99.5% availability rate.
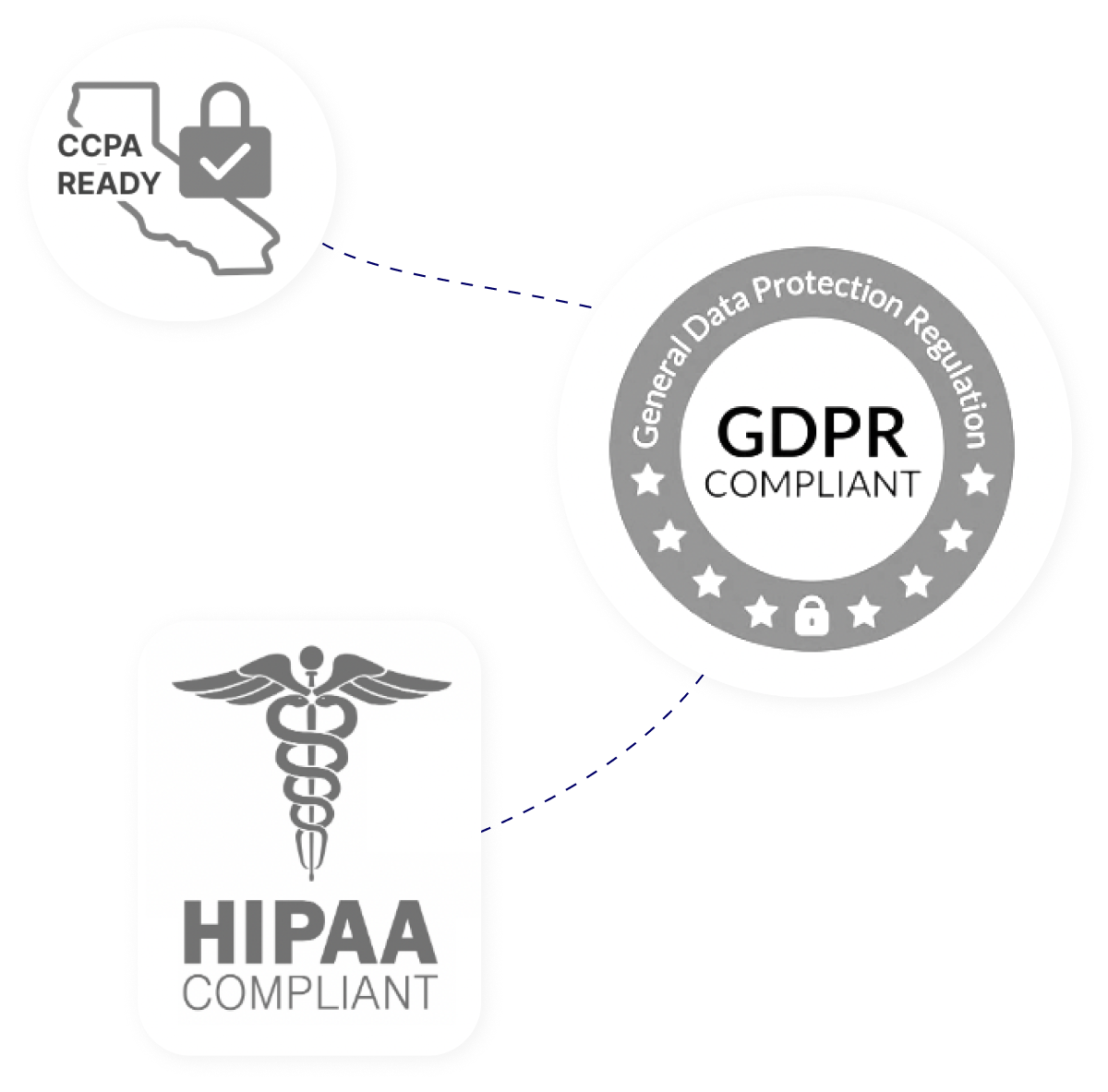
We have summarized how DESelect handles your data. Here are:
DESelect principles are integrated into our security approach, ensuring a company-wide commitment to protecting our customer’s data
- Personal ResponsibilityAt DESelect, the principle of personal responsibility is upheld through regular security awareness trainings, ensuring that everyone is equipped with the knowledge and skills to meet and maintain the highest security standards.
- Continuous ImprovementDESelect’s commitment to continuous improvement includes prioritizing security by partnering with INTIGRITI for a bug bounty program, inviting the community to test our security measures and reward individuals who identify bugs.
- TrustDESelect’s principle of TRUST embodies a commitment to prioritize security and privacy by design, ensuring that data protection measures are integrated into every aspect of their operations, products, and services.
- AdaptabilityAt DESelect, we prioritize adaptability by continually assessing and improving our security practices based on the most relevant and up-to-date industry standards. We believe that this approach allows us to provide our clients with robust security measures of protection against potential security threats and to stay ahead of emerging security risks.
- Customer ExperienceDESelect prioritizes the customer experience by ensuring that our security & privacy team is available 24/7 to promptly address any questions, concerns or incidents.
Frequently Asked Questions
-
What data do you store?
DESelect Segment does not store your customer data. We only store certain pieces of “metadata”, such as the name of a data extension. To learn more about how we handle data, visit our security portal.
-
Are you compliant with data privacy compliance regulations such as GDPR and CCPA?
Yes. To learn more about DESelect and data privacy, visit our privacy and cookie policy page.
-
Do you use encryption protocols when transferring data? If yes, which ones?
Traffic to and from the DESelect servers is secured through TLS based connectivity. The DESelect service always requires SSL/TLS between the client (browser, mobile apps, ...) and the server. Also, all communication between DESelect and the Marketing Cloud API happens over TLS 1.3.
Administrative functions towards DESelect servers in the data center are performed over encrypted channels. These include SSH and TLS.
-
What is your policy / SLA on breach notifications?
DESelect will inform the customer in case of data breach or suspected data breach. Breach
notifications will take place within 24 hours of detection of the incident. -
Have you experienced a cybersecurity event in the past two years?
No, DESelect has never had any cybersecurity incident.
-
Are you covered by any cybersecurity insurance?
Yes, our cyber security insurance covers damages up to 500.000 euro, and provides benefits such as instant support from security experts in case of a data leak.
-
What does the Salesforce Security Review entail?
Before accepting applications on the AppExchange, Salesforce does a thorough security review of each application. During this review, they scan the app for security vulnerabilities. Besides the initial review, Salesforce also does random checks throughout the year. If apps are found to have vulnerabilities after being released on the AppExchange, developers will be made aware and the app will be removed from the AppExchange if the vulnerabilities are not fixed quickly.
Unfortunately, Salesforce does not provide a report of the initial or follow-up security reviews. However, we know the review entails both automated tests (like the ZAP scanner) and manual tests (like SQL injection tests).
Below are some resources that provide more information regarding this security review: